When clients invest in a business application, they need to know that their data is protected and separated from other clients’ data; This is what security specialists refer to as boundary protection. Although Dynamics 365 and Power Platforms are SaaS solutions and the platform is Microsoft’s responsibility, we are required to understand how this is set up over Azure.
Dynamics 365 security
The article mentions physical and logical data segregation in Microsft’s post on Dynamics 365 Security.
- Physical and logical network boundaries with strictly enforced change control policies.
- Segregation of duties that require a business need to access an environment.
- Highly restricted physical and logical access to the cloud environment.
https://docs.microsoft.com/en-us/dynamics365/get-started/security
However, the article doesn’t cover how the network physical and logical segregation are configured. This article will try to explain how the infrastructure is built.
Protecting Data and Privacy in the Cloud
In Microsoft’s publication “Protecting Data and Privacy in the Cloud”, we can clearly understand the difference in the level of control that the clients have over SaaS systems compared to IaaS and PaaS.
The hardware and software details of the components are not shared with the end customers when using a SaaS solution such as Dynamics 365 and Power Platforms.
To download the report, check the link.
Or directly download the link for D365Update.com.
Microsoft-managed service
Dynamics 365 production infrastructure is hosted as a Microsoft-managed service, and the hardware and software details of the components are not shared with the end customers. However, the diagram below illustrates the Dynamics 365 for Customer Engagement infrastructure components; this information is provided for illustration purposes only and is subject to change.
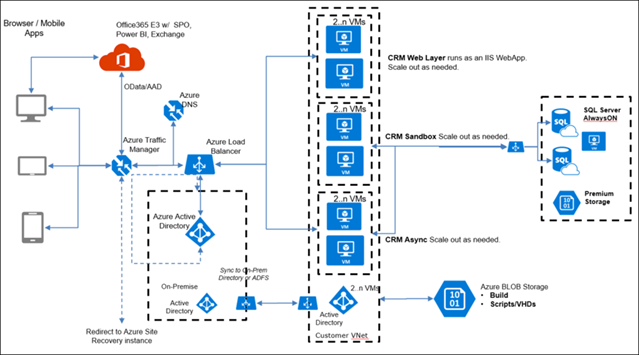
The diagram shows segregation using VNets for each environment, which resides in a customer-segregated VNet.
Dynamics 365 Boundary Protection
The first is data access controls. Data access controls fall into two categories: physical and logical. On the physical side, access to data center facilities is guarded by outer and inner perimeters with increasing security at each level, including perimeter fencing, security officers, locked server racks, multi-factor access control, integrated alarm systems, and extensive 24×7 video surveillance from the operations center.
Access to customer data is restricted based on business needs. Access is restricted by controls such as role-based access control, two-factor authentication, minimizing standing access to production data, and logging and auditing of activities performed in the production service environment.


